Example
Input ciphertext: "QEB NRFZH YOLTK CLU GRJMP LSBO QEB IXWV ALD"
Input word: "fox"
Output plaintext: "the quick brown fox jumps over the lazy dog"
Ever since ancient civilizations could write letters to each other, people have wanted to keep some messages secret in case they were intercepted by someone else. To do this, they used an encryption scheme or secret code to encrypt their message before sending it. The receiver could then decrypt it and read it if they knew how to decrypt it. In cryptography the original unencrypted message is called the plaintext (usually shown in all lowercase) while the encrypted message is the ciphertext (SHOWN IN ALL UPPERCASE).
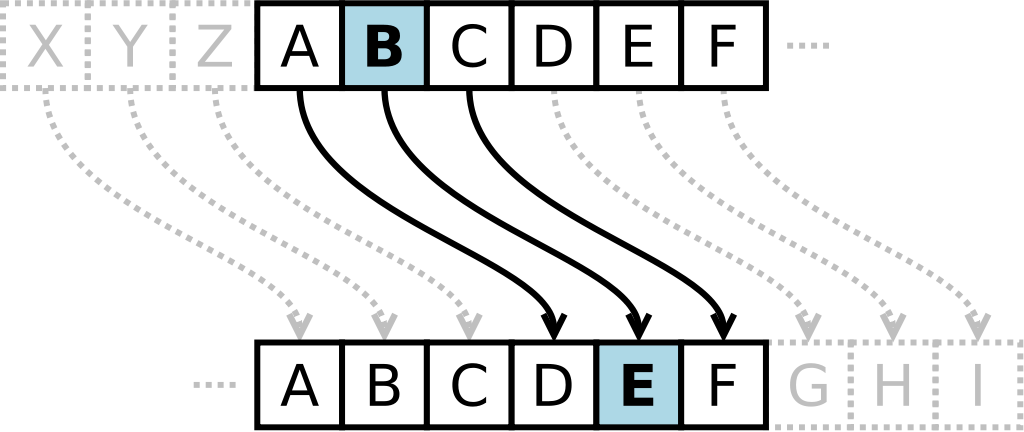
A famous method of encrypting a message is the Caesar cipher. It involves using a shifted alphabet instead of the regular alphabet. For example, a shift of 13 will involve changing A to N, B to O, C to P, and so on. It is a very weak cipher that provides no security nowadays but was actually secure at the time when no one knew of cryptography.
If you knew even a single word that is present in the ciphertext, that would be enough to break the caesar cipher and reveal the secret message. Given the ciphertext and a word that definitely exists in the plaintext, return the plaintext message.
Input: The ciphertext to be decrypted, and one word that is present in the plaintext.
Output: The original message in lower case letters.
| Difficulty | Timesink | ||
|---|---|---|---|
| Function | break_caesar_cipher(ciphertext, known_word) | ||
You must be logged in to view your submissions.
Let us know what you think about this problem! Was it too hard? Difficult to understand? Also feel free to discuss the problem, ask questions, and post cool stuff on Discourse. You should be able see a discussion thread below. Would be nice if you don't post solutions in there but if you do then please organize and document your code well so others can learn from it.